You may have heard of click-to-play plugins (in short: don’t load plugins until they’re clicked). You may have also heard of the blocklist (essentially a list of addons and plugins that are disabled to prevent users coming to harm; this includes vulnerable and outdated versions of popular plugins). Now, appearing together for the first time in Firefox Beta, allow me to introduce click-to-play blocklisted plugins!
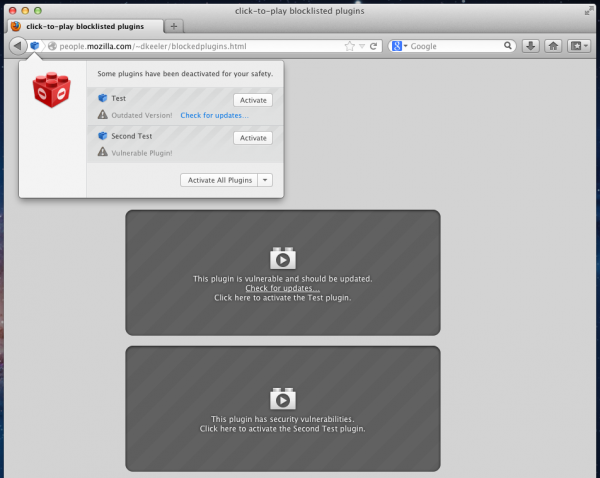
This is how it looks in action:
(Note that the popup notification won’t show itself automatically. This is intentional, so as to not interrupt the user. To open the popup, simply click the plugin icon in the url bar as shown below.)
![]()
By combining the safety of the blocklist with the flexibility of click-to-play, we now have an even more effective method of dealing with vulnerable or out-of-date plugins. Instead of choosing between vulnerable but useful (by allowing an old plugin to run automatically) and safe but less useful (by completely disabling old plugins), click-to-play blocklisted plugins gives the user the ability to make an informed decision depending on their current activity. For instance, when browsing a reputable video sharing website, a user might feel safe enough to enable a vulnerable plugin in order to view the site’s content (in fact, the trusted site can be whitelisted using the “Always activate plugins for this site” option in the button drop-down menu). Of course, it would be best if the user upgraded the plugin to a secure version, but perhaps they can’t for one reason or another. In another scenario, they might not fully trust a site they arrive at after visiting a link sent from a friend. In this case, the blocklisted plugin would not automatically run, and the user would be protected.
At the moment, click-to-play blocklisted plugins is a security feature that protects against drive-by attacks targeting plugins that are known to be vulnerable. It does not prevent attacks where a user is convinced to activate a vulnerable plugin on a malicious site. It also is not an all-purpose plugin management system.
This feature is enabled by default, so users are automatically protected. For the adventurous, the about:config preference “plugins.click_to_play” can be set to true to enable click-to-play for all plugins, not just out-of-date ones. However, this aspect of the feature is still in development.
This feature is currently in Firefox Beta, so grab a copy. For more information about the specific plugins we’re starting with, visit the add-ons blog. There is also more information in a few bugs.
Dimas wrote on
wrote on
gewb wrote on
wrote on
Bah wrote on
wrote on
Gianni wrote on
wrote on
Matt wrote on
wrote on
dup wrote on
wrote on
Gianni wrote on
wrote on
Quang Đức wrote on
wrote on
Alexey Trunev wrote on
wrote on
Guest wrote on
wrote on