Mozilla is changing the way Firefox loads third party plugins such as Flash, Java and Silverlight. This change will help increase Firefox performance and stability, and provide significant security benefits, while at the same time providing more control over plugins to our users.
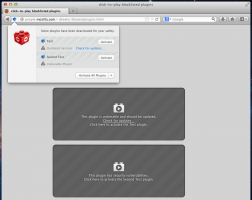
Previously Firefox would automatically load any plugin requested by a website. Leveraging Click to Play Firefox will only load plugins when a user takes the action of clicking to make a particular plugin play or the user has previously configured Click To Play to always run plugins on the particular website.
More User Control
Users should have the choice of what software and plugins run on their machine. Click to Play allows users to easily choose if they wish to run a plugin on a particular site. Users can also configure sites to never run plugins or conversely always run plugins. This change puts the user in control.
Increased Performance & Stability
Poorly designed third party plugins are the number one cause of crashes in Firefox and can severely degrade a user’s experience on the Web. This is often seen in pauses while plugins are loaded and unloaded, high memory usage while browsing, and many unexpected crashes of Firefox. By only activating plugins that the user desires to load, we’re helping eliminate pauses, crashes and other consequences of unwanted plugins.
Significant Security Benefits
One of the most common exploitation vectors against users is drive by exploitation of vulnerable plugins. In this kind of attack, a user with outdated or vulnerable plugins installed in their browser can be infected with malware simply by browsing to any site that contains a plugin exploit kit. We’ve observed plugin exploit kits to be present on both malicious websites and also otherwise completely legitimate websites that have been compromised and are unknowingly infecting visitors with malware. In these situations the website doesn’t have any legitimate use of the plugin other than exploiting the user’s vulnerable plugin to install malware on the their machine. The Click to Play feature protects users in these scenarios since plugins are not automatically loaded simply by visiting a website.
In addition to the security benefits provided by Click to Play Mozilla also strongly recommends that users keep their plugins up to date. The following website can be used to determine if plugins are current.
https://www.mozilla.org/plugincheck/
Implementing this change
Our plan is to enable Click to Play for all versions of all plugins except the current version of Flash. Click to Play has already been enabled for many plugins that pose significant security or stability risks to our users. This includes vulnerable and outdated versions of Silverlight, Adobe Reader, and Java.
More specifically, our next steps are the following:
1. Click to Play old versions of Flash (versions <=10.2.*) and slowly add more recent insecure Flash versions to the Click to Play list. Note: The most current version of Flash will NOT have Click To Play.
After we complete final UI work:
2. Click to Play current versions of Silverlight, Java, and Acrobat Reader and all versions of all other Plugins.
During this change we will monitor the results and feedback of the new settings and UI to ensure we’re providing a quality experience and delivering the many benefits of Click to Play to Firefox users.
Michael Coates
Director of Security Assurance
PlugIn McAddOn. wrote on
wrote on
philipp wrote on
wrote on
Curtisk wrote on
wrote on
Daniel Veditz wrote on
wrote on
Asbjørn wrote on
wrote on
Daniel Veditz wrote on
wrote on
Use NoScript wrote on
wrote on
Felix wrote on
wrote on
John Schoenick wrote on
wrote on
a wrote on
wrote on
webuser wrote on
wrote on
Xan Charbonnet wrote on
wrote on
Dimas wrote on
wrote on
LOGAN wrote on
wrote on
Danny Moules wrote on
wrote on
Anonymous-783 wrote on
wrote on
Chris wrote on
wrote on
Anonym wrote on
wrote on
Kyle wrote on
wrote on
TomH wrote on
wrote on
Georg Fritzsche wrote on
wrote on
NotAmused wrote on
wrote on
Michael Kaply wrote on
wrote on
Macromedia wrote on
wrote on
tim ashman wrote on
wrote on
Richie Hindle wrote on
wrote on
Richie Hindle wrote on
wrote on
Georg Fritzsche wrote on
wrote on
Richie Hindle wrote on
wrote on
Martin Husemann wrote on
wrote on
Anony123456 wrote on
wrote on
Axis wrote on
wrote on
Neyland wrote on
wrote on