Firefox 61 will block subresource loads that rely on the insecure FTP protocol unless the document itself is an FTP document. For example, Firefox will block FTP subresource loads within HTTP(S) pages.
The File Transfer Protocol (FTP) enables file exchange between computers on a network. While this standard protocol is supported by all major browsers and allows convenient file sharing within a network, it’s one of the oldest protocols in use today and has a number of security issues.
The fundamental underlying problem with FTP is that any data transferred will be unencrypted and hence sent across networks in plain text, allowing attackers to steal, spoof and even modify the data transmitted. To date, many malware distribution campaigns rely on compromising FTP servers, downloading malware on an end users device using the FTP protocol. Further, FTP makes HSTS protection somewhat useless, because the automated upgrading from an unencrypted to an encrypted connection that HSTS promises does not apply to FTP.
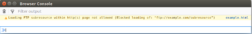
Following through to our intent to deprecate non-secure HTTP and aligning with Mozilla’s effort to improve adoption of HTTPS Firefox will block subresource loads, like images, scripts and iframes, relying on the insecure FTP protocol. Starting with Firefox 61, loading an FTP subresource within a non-FTP document will be blocked and the following message will be logged to the console:
For the Mozilla Security Team:
Tom Schuster and Christoph Kerschbaumer