Content Strategy in Action on Firefox for Android
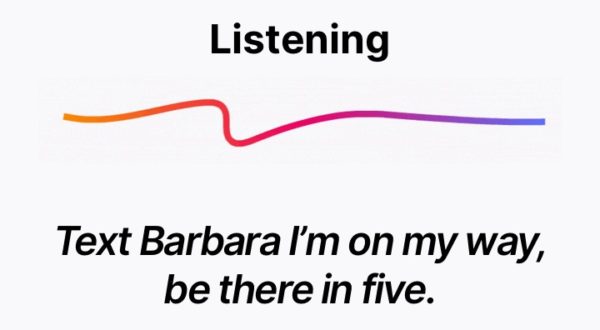
The Firefox for Android team recently celebrated an important milestone. We launched a completely overhauled Android experience that’s fast, personalized, and private by design. When I joined the mobile team … Read more